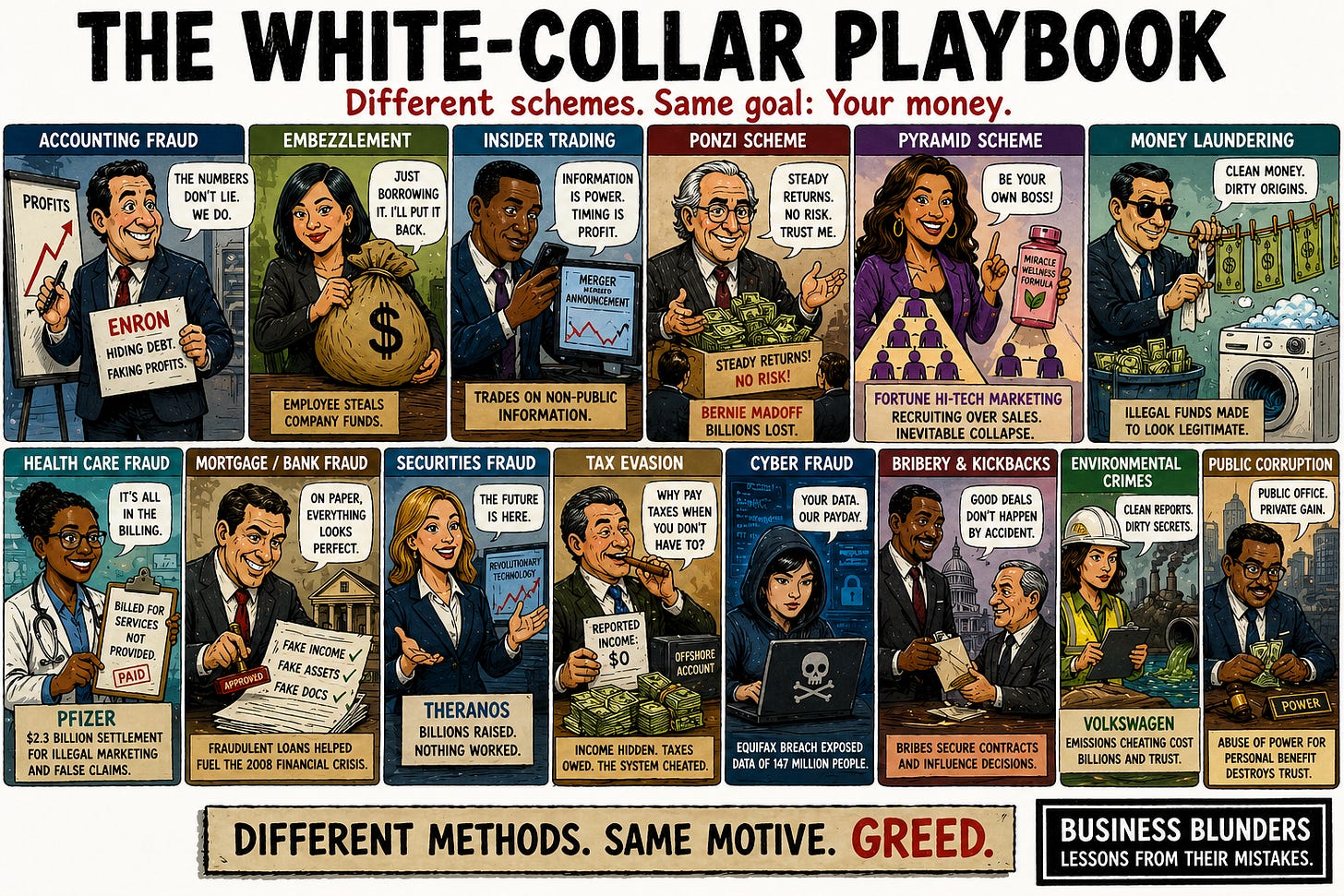
The White-Collar Playbook
The most common types of financial fraud and the companies that didn't get away with them.
Most people in business do not start out with plans to defraud, but under pressure, they may end up committing some of the most common types of financial fraud.
Sometimes they may not even realize how far they’ve crossed the line until it’s too late.
Bad choices may seem inconsequential at first, like handy little shortcuts to prosperity. But when they’re justified, repeated and scaled, they can explode, destroying companies and careers, and notching their place in the Blunder Lists.
The Most Common Types of Financial Fraud
White-collar frauds follow repeating patterns throughout history. In their quests to succeed, compete or simply avoid insolvency, even the smartest executives can suffer moral and legal failures. Different industries, different executives, same playbook.
Here’s a look the most common types of financial fraud deployed by companies and executives, and blowups that followed.
Table Of Contents
Part 1. Frauds That Hurt Investors
Accounting fraud: Faking the numbers
When a business underperforms, the temptation is simple: Let the numbers tell a different story. That means inflated revenue, hidden debt, and accounting tricks designed to mislead investors and regulators.
Some of the most notorious accounting fraud examples include:
Enron – Used off-balance-sheet partnerships to bury losses until the entire structure collapsed.
Bernie Ebbers (Worldcom) – Oversaw an accounting fraud that inflated earnings by billions.
Computer Associates – Used “35-day months” to keep the books open longer and record additional revenue.
Crazy Eddie (Eddie Antar) –Bolster books for an initial public stock offering by ending a skimming scheme and counting the money as growth.
Bayou Group – Created a fake accounting firm to issue phony books.
The numbers don’t have to be real. They just have to hold up long enough.
Earnings manipulation: Managing the quarter, not the business
Companies smooth results by shifting revenue and earnings into one quarter or another. They may delay losses or rely on one-off adjustments to hit expectations. Sometimes they fake inventories or ship products to warehouses and count them as sales.
These earnings manipulation examples show how companies manage the quarter instead of the business:
Q.T. Wiles (MiniScribe) – Inflated inventory by shipping boxes of bricks as “hard drives” in one of the most egregious examples of earnings manipulation.
“Chainsaw Al” Dunlap (Sunbeam) – Used aggressive channel stuffing to pull forward revenue and hit quarterly targets.
Waste Management – Manipulated depreciation and assets to smooth earnings and avoid recognizing expenses.
Xerox – Pulled forward revenue from long-term leases to meet Wall Street expectations
The goal isn’t to improve the business. It’s to make the quarter look just good enough.
Securities and investment fraud: Selling stories, not reality
Investors are sold a vision that doesn’t match the underlying business. That can mean exaggerated performance, hidden risks, or entirely fabricated technology. It often begins as a fake-it-’til-you-make it strategy but runs out of time. And sometimes it’s a coverup for executives misappropriating money.
Here are some examples of securities and investment fraud:
John Rigas (Adelphia Communications) – Concealed billions in off–balance-sheet debt, misleading investors about the company’s financial condition.
Jordan Belfort (Stratton Oakmont) – Hyped worthless stocks to investors in classic “pump-and-dump” schemes.
Allen Stanford (Stanford Financial) – Marketed high-yield CDs as safe investments backed by solid assets; in reality, funds were misused in a massive fraud.
Sandy John Masselli (Carlyle Entertainment) – Solicited at least $3 million in investments for an upcoming initial public stock offering, but his company never even filed an application for an IPO.
The business doesn’t have to be profitable. The story just has to hold.
Insider trading: Profiting from non-public information
Why guess what the market will do when you already know? Insider trading turns confidential information about earnings results, mergers, regulatory decisions into guaranteed gains. It’s illegal for corporate executives and other insiders to trade on material, non-public information.
Some of the most infamous insider trading examples include:
Rajat Gupta (Goldman Sachs) – Tipped a hedge fund manager about confidential boardroom decisions, including Berkshire Hathaway’s investment.
Raj Rajaratnam (Galleon Group) – A case that intersects with Gupta. Built a network trading on inside tips across corporate America.
Michael Milken (Drexel Burnham Lambert) – An icon of 1980s greed and a central figure in the junk bond era.
Joseph Nacchio (Qwest) – Sold millions in stock while aware of undisclosed business risks.
The edge isn’t always insight. It’s access, until access becomes evidence.
Part 2: Theft From Inside
Embezzlement: Pinching the pot
Money is entrusted to an employee, executive or advisor, then quietly redirected. Often, it’s disguised as routine transactions, reimbursements, or temporary transfers that never come back. The common thread is access, and the belief no one is watching closely enough.
Embezzlement is blatant theft, and all-too-common. Examples include:
Shan Hanes (Heartland Tri-State Bank) – A small-town bank CEO who bankrupted his institution while becoming a fraud victim himself.
Dennis Kozlowski (Tyco) – Looted more than $100 million through unauthorized bonuses, art purchases, and company-funded extravagances.
Michael “Mickey” Monus (Phar-Mor) – Diverted hundreds of millions to cover losses and maintain the illusion of profitability.
Tom Girardi (attorney) – Embezzled millions from needy clients of his law firm.
The crime isn’t complicated. The safe doors were left wide open.
Procurement and vendor fraud: Faking Invoices, taking bribes
There are plenty of ways for company insiders to establish a fraudulent side hustle. They may inflate invoices or even create bills from vendors that don’t exist at all. They may take kickback or bribes, steering contracts to “friendly” vendors, instead of the lowest bidders. The result is a system where outcomes are bought, not earned.
Examples of procurement and vendor fraud include:
Lester T. Jones (Atlanta Hawks) – Full Court Heist – Used fake invoices to siphon off $3.7 million for his personal use.
Michael Kali (Netflix) – Took bribes and kickbacks from vendors seeking contracts from the streaming giant.
Goldman Sachs – Paid more than $1 billion in bribes to Malaysian and Abu Dhabi officials to obtain billions worth of bond offerings.
ComEd – Paid allies of former Illinois House Speaker Michael Madigan $1.3 million for little or no work to influence legislation.
Walmart – Paid bribes to accelerate store growth in Mexico, Brazil, India and China.
It’s not the lowest bid that wins. It’s the one that pays the decision makers under the table.
Bid Rigging: Killing the competition before the game begins
Instead of competing, companies that usually bid against each other decide to collude, rotating contract winners amongst themselves, inflating prices, or submitting fake bids to create the illusion of competition.
Bid-rigging likely occurs more often than it’s prosecuted. Here are some bid-rigging schemes that came to light:
Tim Leiwekehe (OakviewGroup) – Accused of rigging the bid for the taxpayer-funded Moody Center at the Austin campus of the University of Texas, but won a pardon from President Donald Trump.
Sotheby’s & Christie’s – Auction houses conspired to fix commissions, eliminating true competition for sellers.
LIBOR scandal (multiple banks) – Traders coordinated submissions to manipulate benchmark interest rates, distorting outcomes tied to competitive pricing across markets.
Wilder Fitness Equipment – Coordinated bids and manipulated the competitive process in contracts for fitness equipment sold to schools, universities and other institutions.
The bids look competitive. The winner is already decided.
Part 3: Ponzis And Pyramids
Ponzi schemes: Paying investors with their own money
No profits. Often not even a real company. Just a recruiting operation. In a Ponzi scheme, early investors get paid with incoming funds, creating the illusion of success, until the money runs out.ran the most infamous version, sustaining a multibillion-dollar fraud for decades before it inevitably collapsed.
Ponzi schemes have been carried out for centuries. Some examples include:
Charles Ponzi (Boston swindler) – Promised high returns from international postal coupons, paying early investors with new money until the scheme collapsed.
Bernie Madoff (Madoff Securities) –Ran the most infamous version, sustaining a multibillion-dollar fraud for decades before it inevitably unraveled.
Tom Petters (Petters Co.) – Fabricated a retail financing business and used new investor funds to pay existing ones.
Eliyahu Weinstein (Optimus Investments) – Raised money for nonexistent real estate deals, using incoming funds to maintain the illusion of returns.
Thomas Nicholas Salzano (National Realty Investment Advisors) – Ran commercials on Fox News to attract victims for a $658 million fraud.
It’s not really a business or an investment strategy. Just a promise looking for the next unwary investor.
Pyramid schemes: Recruitment disguised as a business
Unlike a Ponzi scheme, a pyramid scheme doesn’t pretend to invest money. It pretends it’s a business. Participants pay to join, then earn money primarily by recruiting others who pay to join, who then recruit more participants. The product, if there is one, is usually a prop or something that is easily available elsewhere. The structure works as long as the base keeps expanding. But it usually can’t.
Some of the most notable pyramid scheme examples include:
IM Mastery Academy – Marketed as a trading education platform, but income for many participants depended heavily on recruiting new members.
Herbalife – After critics called it a pyramid scheme, regulators found the multilevel marketing firm relied heavily on recruiting rather than genuine retail demand.
Fortune Hi-Tech Marketing – Sold access to telecom and utility services while rewarding recruitment over actual product sales.
BurnLounge – Claimed to sell online mustic stores, but compensation was primarily tied to recruiting.
The product isn’t the business. The next recruit is.
Part 4: Financial System Abuses
Compliance failures: Looking the other way
Financial institutions are supposed to flag suspicious activity, verify accounts, and stop illicit flows. When they don’t, they become part of the system, whether it’s intentional or not.
Examples of compliance failure:
Brinks – Moved large sums of cash domestically and across the Southwest border without required controls.
Bank Of America – Settled lawsuits alleging that is helped enable Jeffrey Epstein’s sex-trafficking operation.
HSBC – Paid a massive penalty after failing to stop money laundering tied to drug cartels and sanctioned countries, despite clear red flags.
Danske Bank (Estonia branch) – Mislead U.S. financial institutions as it processed vast sums of suspicious non-resident funds with weak anti-money-laundering controls.
The warning signs are there. The system turns a blind eye.
Bank fraud: Lying for loans
Fake income, concoct assets, misrepresent risks and apply for a loan. Mortgage fraud played a central role in the 2008 financial crisis as lenders approved loans based on unreliable or fabricated information. When defaults rose, the system realized it had been built on bad assumptions and bad data.
Some of the most egregious bank fraud examples include:
First Brands Group – Accused of taking out loans based on phony collateral and double pledging receivables.
Tricolor Holdings – Charged with misrepresenting loan performance and underlying collateral to obtain financing.
Countrywide Financial – Falsified borrower income and documentation to push through mortgages that didn’t meet standards.
Lee Farkas (Taylor, Bean & Whitaker) – Orchestrated a massive scheme selling banks fake or double-pledged mortgage assets to secure funding.
Todd and Julie Chrisley (Reality TV) - Convicted for defrauding banks out of more than $30 million.
If phony numbers get you the loan, the truth can wait.
Part 5: Defrauding Government and Public Systems
Healthcare fraud: Billing for what didn’t happen
Charge for unnecessary services. Inflate legitimate ones. Or bill for treatments that never occurred. The scale can be enormous because the system processes massive volumes of claims. But these cases are practically routine.
Some of the most heartless healthcare fraud examples include:
HCA Healthcare – Billed for unnecessary services and paid kickbacks to drive referrals, inflating Medicare, Medicaid, and TRICARE reimbursements.
Pfizer – Illegally promoted off-label uses of drugs, leading to improper billing of federal healthcare programs.
Zynex Medical – Accused of fraudulently over-billing insurers and the U.S. government through excessive and unnecessary claims.
Tenet Healthcare – Paid kickbacks for patient referrals and billed federal programs for services tied to those arrangements.
The patient is the pretext. The bill is the business.
Tax Evasion: Cheating the taxman
Income goes unreported. Deductions are fabricated. Money is moved offshore without disclosure. Unlike legal tax avoidance, this crosses into deception, misleading authorities to reduce or eliminate tax obligations.
Some notable tax evasion cases include:
Robert T. Brockman (entreprenuer) – Spent the final years of his life fighting the IRS but lost in death when his estate finally paid.
RCI Hospitality Holdings – The world’s largest strip club operator accused of bribing a public tax auditor to escape paying sales taxes.
Michelle O’Connor – A Kansas City Realtor indicted for allegedly founding a two-member church to dodge $40,000 in taxes.
Wade Cook (business book author) – Evaded federal income tax on $9.5 million in royalties and filed false tax returns.
Sam Waksal (Imclone) – Before he was famously convicted in an insider trader scheme involving his friend, Martha Stewart, he pleaded guilty two criminal charges for dodging $1.2 million in sales tax on $15 million worth of artwork.
You can hide the money. The IRS may still find it.
Public corruption: Government offices for personal gain
Public power becomes a private asset. Officials steer contracts, influence policy, or abuse authority for financial benefit. It undermines not just individual institutions, but trust in the system itself.
Michael Madigan (llinois House Speaker) – Convicted in a sweeping corruption case alleging he traded official actions for jobs, contracts, and other benefits through political allies.
Jack Abramoff (Lobbyist) – Defrauded American Indian tribes seeking influence for their casinos and corrupted public officials with gifts, trips and favors.
Paul Manafort – Concealed millions in overseas income through offshore accounts and shell companies while secretly advancing the interests of pro-Russia political figures.
Duke Cunningham (U.S. Congress) – Accepted millions in bribes from defense contractors in exchange for steering government contracts.
Rita Crundwell (City of Dixon, Ill.) – Created fake vendor accounts and siphoned tens of millions in public funds over decades.
Kwame Kilpatrick (Detroit mayor) – Used public office for personal enrichment and was convicted on corruption charges.
Public office is not private property.
Part 6: Corporate Misconduct
Environmental crimes: Cutting costs by trashing the planet
Compliance is expensive. Violations are cheaper, at least in the short term. Companies may falsify emissions data, dump waste illegally, or ignore environmental safeguards to protect profits.
Some of the most heinous environmental crime cases include:
Volkswagen (Dieselgate) – Installed software to cheat emissions tests, triggering one of the most expensive pollution scandals in history.
BP (Deepwater Horizon) – Cost-cutting and safety failures led to a catastrophic oil spill in the Gulf of Mexico, with lasting environmental damage
Exxon (Exxon Valdez) – Negligence led to what was then the largest oil spill in U.S. history, resulting in massive environmental harm and cleanup costs.
PG&E (groundwater contamination) – Dumped 370 million gallons of toxic wastewater into unlined ponds at its Hinkley, Calif., compressor station, allowing the effluent to seep into groundwater.
It’s cheaper to break the rules, until the bill for the damages comes due.
Intellectual property theft: Stealing the competitive advantage
Trade secrets, proprietary systems and protected designs are taken without permission. It’s faster than building something from scratch, and often framed internally as “leveling the playing field.” When exposed, it becomes a costly legal and reputational disaster.
Some of the most notable intellectual property theft cases include:
Huawei (vs. T-Mobile) – Huawei employees allegedly photographed and attempted to remove parts of T-Mobile’s “Tappy” the robot while violating confidentiality agreements with the wireless carrier.
Samsung (vs. Apple) – Found to have copied key design elements and features of the iPhone, leading to a multibillion-dollar legal battle over smartphone patents.
Waymo vs. Uber (Anthony Levandowski) – Self-driving car trade secrets were taken and used to accelerate development at a competitor, resulting in a high-profile settlement.
Kolon Industries – Stole trade secrets from DuPont related to Kevlar production, leading to major damages and a guilty pleading to criminal charges.
Why build it when you can just take it? Because lawsuits and prosecutions could cost you more.
Part 7: Digital Fraud
Cybercrime and computer fraud: Digital access, real-world damage
Phishing, hacking, ransomware, and data breaches can expose millions of records or shut down entire operations. The costs technical financial, legal and reputational.
Some of the biggest cybercrime and computer fraud cases include:
Equifax – Suffered a massive data breach that exposed sensitive information on millions of consumers, turning a security failure into a corporate crisis.
Target – Attackers infiltrated the payment system through a third-party vendor, compromising millions of credit and debit card accounts.
Heartland Payment Systems – One of the largest breaches of payment data, exposing millions of credit card numbers later used for fraud.
Colonial Pipeline – Ransomware attack forced a shutdown of fuel distribution across the U.S. East Coast, showing how digital breaches can disrupt physical infrastructure.
Sony Pictures – Hacked by a state-linked group, resulting in leaked data, internal communications, and major operational disruption.
The system goes down. The damage goes everywhere.
Credit card fraud: Cashing in on personal data
Credit card fraud is often the endgame of most data breaches. Fraudsters use stolen personal data to open new lines of credit, drain existing ones, or make unauthorized purchases at scale. The damage spreads quickly, and it’s difficult to fully unwind once the data is out.
Some of the largest identity theft and credit card fraud cases include:
Wells Fargo – Employees created millions of unauthorized customer accounts using existing client information to meet internal sales targets.
New Jersey Credit Card Fraud Ring – A sprawling international credit card fraud and money laundering scheme that allegedly caused more than $200 million in losses using stolen credit card data, shell companies and fraudulent transactions.
Albert Gonzalez – One of the largest credit card theft rings in history, stealing tens of millions of card numbers for resale and fraud
Max Butler – Trafficked millions of stolen credit card numbers through underground marketplaces.
Once the data is gone, it’s never solely yours again.
Part 8: How Fraud Gets Charged
Money laundering: Cleaning dirty money
Illegal profits are only useful if they can be spent without raising suspicion. So the money moves through shell companies, real estate, financial institutions until its origins are successfully obscured. Money laundering is often an add-on charge for prosecutors as they build their cases.
Common examples of money laundering:
Changpeng Zhao (Binance) – Failed to maintain anti-money-laundering controls and allowed transactions involving sanctioned nations, including Iran.
Rick Singer (Varsity Blues) — Coordinated bribes, fake athletic credentials and sham charitable payments to help wealthy clients secure spots at elite universities.
Sam Bankman-Fried (FTX) – Moved customer funds through affiliated entities in ways that obscured their origin and use, leading to money laundering–related charges.
Greg Lindberg (insurance tycoon) – Diverted funds through complex, circular transactions, leaving policyholders in bureaucratic limbo while courts and guaranty funds cleaned up the wreckage.
Dirty money is easy to track without a thorough laundering.
Wire fraud: The charge that ties it all together
Most fraud runs over wires these day whether its through emails, texts or bank transfers. That’s all prosecutors need to build a case. Wire fraud doesn’t describe a particular scheme itself. It’s just an easy prosecutorial tool and it is usually piled on tip of other charges.
Notable wire fraud cases include:
Marc Rich (Glencore) – Indicted on more than 50 felony counts, including wire fraud, for making oil deals with Iran during the 1979-1981 hostage crisis.in 1983.
Elizabeth Holmes (Theranos) – Convicted of wire fraud for transmitting false claims to investors.
Carlos Watson (Ozy Media) – Charged with wire fraud for misrepresenting company performance and investor interest through electronic communications.
Trevor Milton (Nikola) – Used media appearances and electronic communications to mislead investors about technology capabilities; convicted of wire fraud
Mail fraud: Prosecutors’ old-school playbook
Before email and wire transfers, fraud traveled by mail, and today they still do. Schemes often involve letters, checks and shipments, giving prosecutors an easy hook.
Well-known cases involving mail fraud include:
Barry Minkow — Sent fraudulent invoices, contracts and insurance-restoration documents through the mail to support a massive accounting fraud at ZZZZ Best.
Leona Helmsley — Used mailed false invoices and tax-related documents in schemes involving fraudulent deductions and personal expenses disguised as business costs. Convicted on federal mail fraud and tax charges.
Scott Rothstein (attorney) — Used mailed documents and settlment agreements to sustain a massive Ponzi scheme involving fictitious legal settlements.
Lou Pearlman (Trans Continental) — Sent fraudulent financial statements and investment documents through the mail to keep his scheme alive.
The envelope looks ordinary. But it contains an easily charged crime.